Penetration Testing & Red Teaming
Penetration Testing
Penetration tests are used to verify the security of applications and IT systems by simulating an attack by a hacker. Our OSCP-certified penetration testers use the techniques and tools of a hacker to uncover security vulnerabilities in the IT environment under investigation. This allows a systematic identification of security vulnerabilities across all relevant attack vectors. The attack vectors extend from the network level to the host level (client and server) to the application and the database, where both the architecture and the source code may contain security vulnerabilities.
The primary goal of a penetration test is to develop security measures to address the identified vulnerabilities. These security measures form the basis for defining system and network hardening that meets your system requirements.
Penetration testing approach based on common standards
We offer a structured approach according to established standards. Overall, all our penetration tests are based on the "Implementation Concept for Penetration Tests" of the German Federal Office for Information Security (BSI) to ensure a structured and comprehensible phase-based approach. Depending on the use case, other international standards such as the OWASP Security Verification Standards and the associated OWASP Testing Guides are included in order to examine your IT systems and applications according to best practices.
Whether as a blackbox penetration test without any information or as a whitebox penetration test with access data, architecture information or even source code, together we plan the optimal penetration test for you. Using threat modeling in accordance to STRIDE, we identify potential threats and define a suitable scope. We are also happy to offer you a multi-stage approach, which could, for example, consist of an upstream offsite blackbox penetration test of your external IT infrastructure, a subsequent whitebox penetration test of the same, as well as an onsite penetration test of your internal company network.
With our Purple Team approach, we look at your IT environment not only from the attacker's perspective (Red Team), but also from the defender's perspective (Blue Team) to effectively improve your company's security. The identified vulnerabilities are classified into risk categories using the Common Vulnerability Scoring System (CVSS) and prioritized in a final report. In addition to a management summary, the report includes technical details on the identified vulnerabilities as well as specific recommendations for their remediation. If you wish, we can enter our findings directly into your ticket system to provide your developers with the best possible support in resolving vulnerabilities.
An optional retest can then be used to verify the effectiveness of the implemented security measures. Testing is also performed for newly implemented security vulnerabilities and those that have become known in the meantime, as well as security-related side effects.
Our penetration testing services
- IT-Infrastructures (Onsite & Offsite)
- Web Applications / Web APIs
- Apps (iOS, Android, Windows App)
- Internet of Things (IoT)
- Backend-Systems
- SAP
Red Teaming
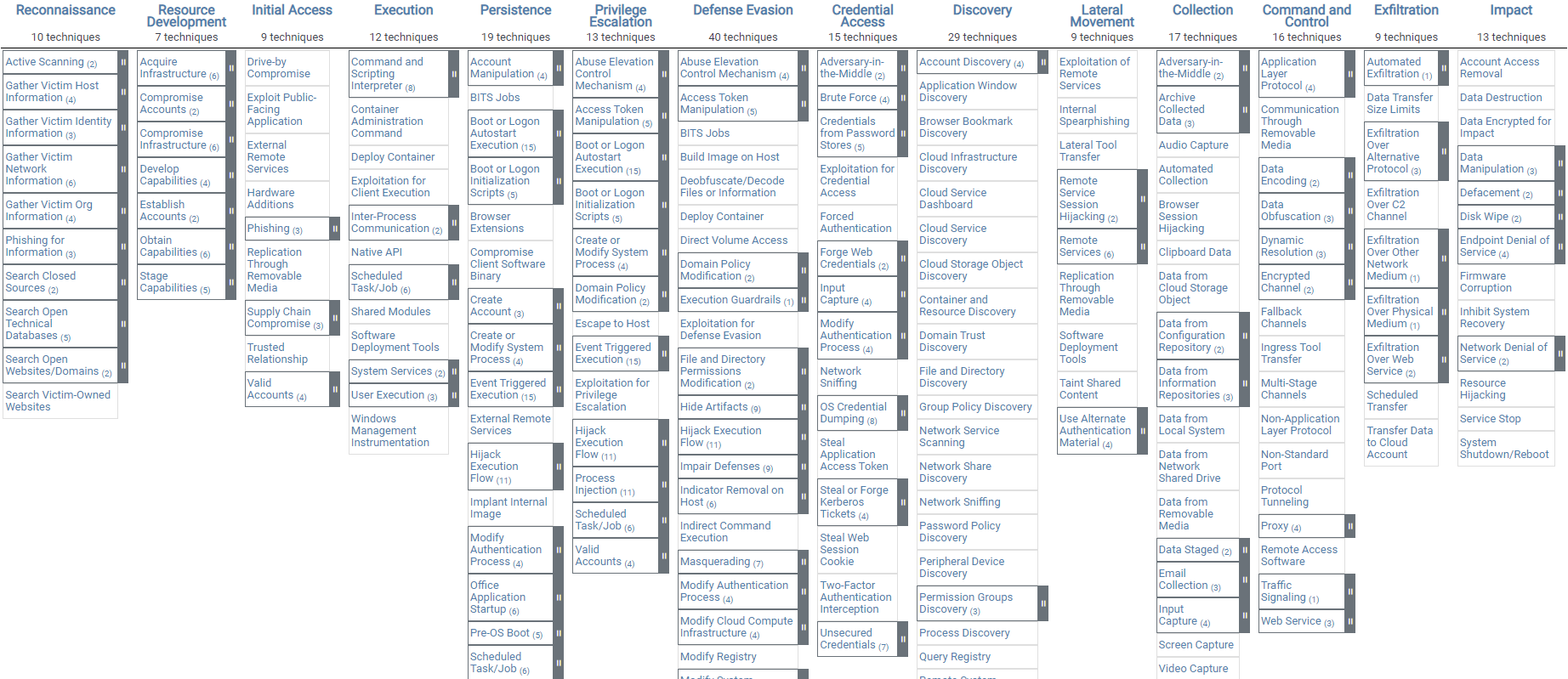
As part of a Red Teaming Assessment, we review the security of your company as a whole from an attacker's perspective. Our goal is to penetrate your corporate network undetected by any means necessary to extract sensitive data, be it through social engineering, physical access, vulnerabilities in IT systems and applications, the use of malware or the bypassing of firewall and antivirus systems. Using the Mitre ATT&CK matrix, we simulate a complex, targeted attack by a professional, organized hacker group (APT simulation).
Red Teaming can reveal not only technical, but also human and organizational vulnerabilities within your organization. Last but not least, such an assessment also shows how well your reactive measures are working in the event of a security incident. Is an attack noticed? Does the Blue Team succeed in isolating the threat? Our Red Teaming Assessment will provide you with answers as well as optimization recommendations.


